AI Grid Security Cameras
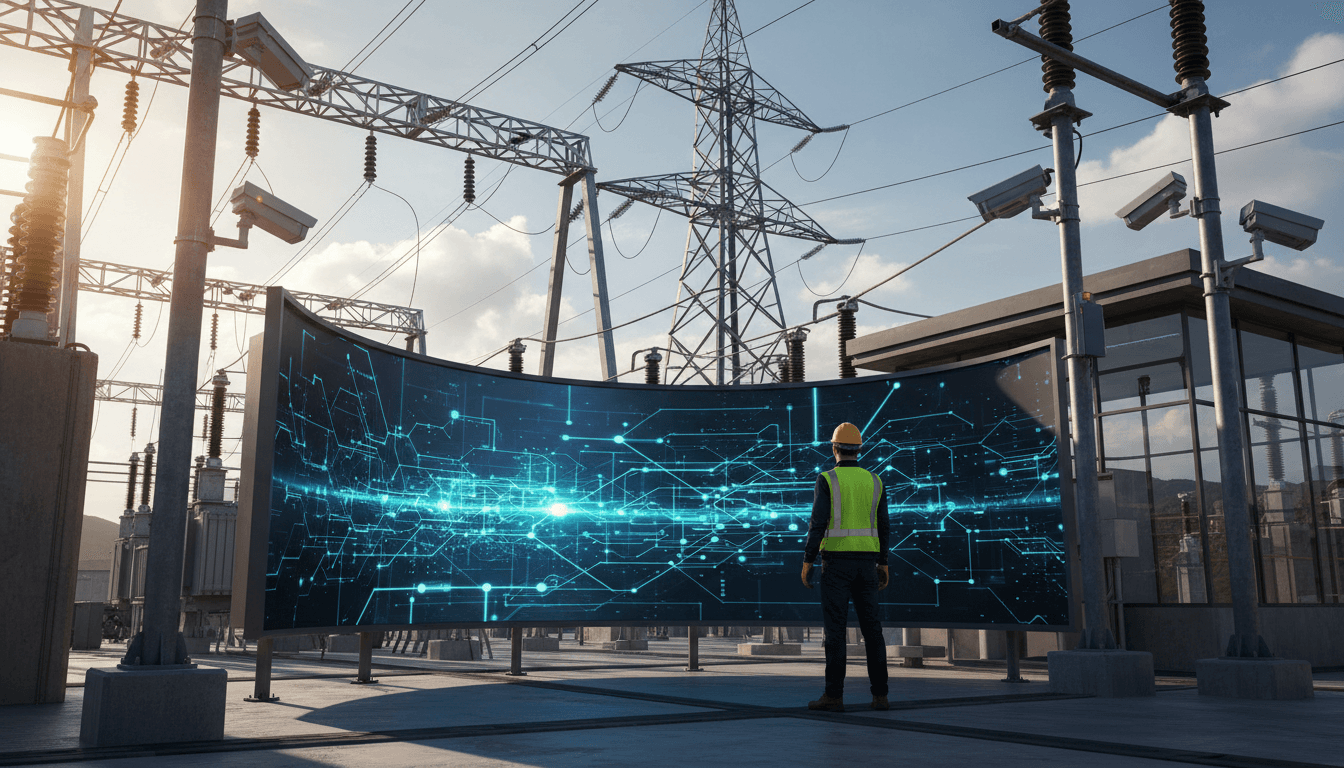
AI Grid Security Cameras represent a pivotal innovation in the Energy and Utilities sector, integrating advanced artificial intelligence to enhance surveillance and security across critical grid infrastructure. These cameras utilize intelligent algorithms to monitor and analyze real-time data, ensuring the protection of assets while optimizing operational efficiency. As energy companies face increasing threats, the relevance of such technology is underscored by the growing necessity for robust security measures that align with broader AI-led transformations in operational strategies.
The implementation of AI Grid Security Cameras is significantly reshaping the Energy and Utilities landscape, driving new competitive dynamics and fostering innovation. By leveraging AI capabilities, organizations can improve decision-making processes, streamline operations, and enhance stakeholder engagement. However, the journey towards full-scale adoption is not without challenges, as companies must navigate integration complexities and evolving expectations. Despite these hurdles, the potential for improved efficiency and strategic growth presents a compelling case for embracing this transformative technology.
Elevate Your Security with AI-Driven Grid Surveillance
Energy and Utilities companies should strategically invest in partnerships focused on AI Grid Security Cameras to enhance surveillance capabilities and data analytics. This approach is expected to drive significant operational efficiencies, reduce risks, and strengthen market competitiveness through proactive threat detection and management.
How AI Grid Security Cameras are Transforming Energy and Utilities?
Implementation Framework
Evaluate existing security frameworks and technologies
Implement advanced analytics for threat detection
Educate staff on AI-driven security protocols
Implement ongoing surveillance and analytics
Regularly review AI effectiveness and strategies
Conduct a thorough assessment of current security infrastructure, identifying gaps and areas for AI integration . This ensures optimal deployment of AI Grid Security Cameras, enhancing overall energy sector security and efficiency.
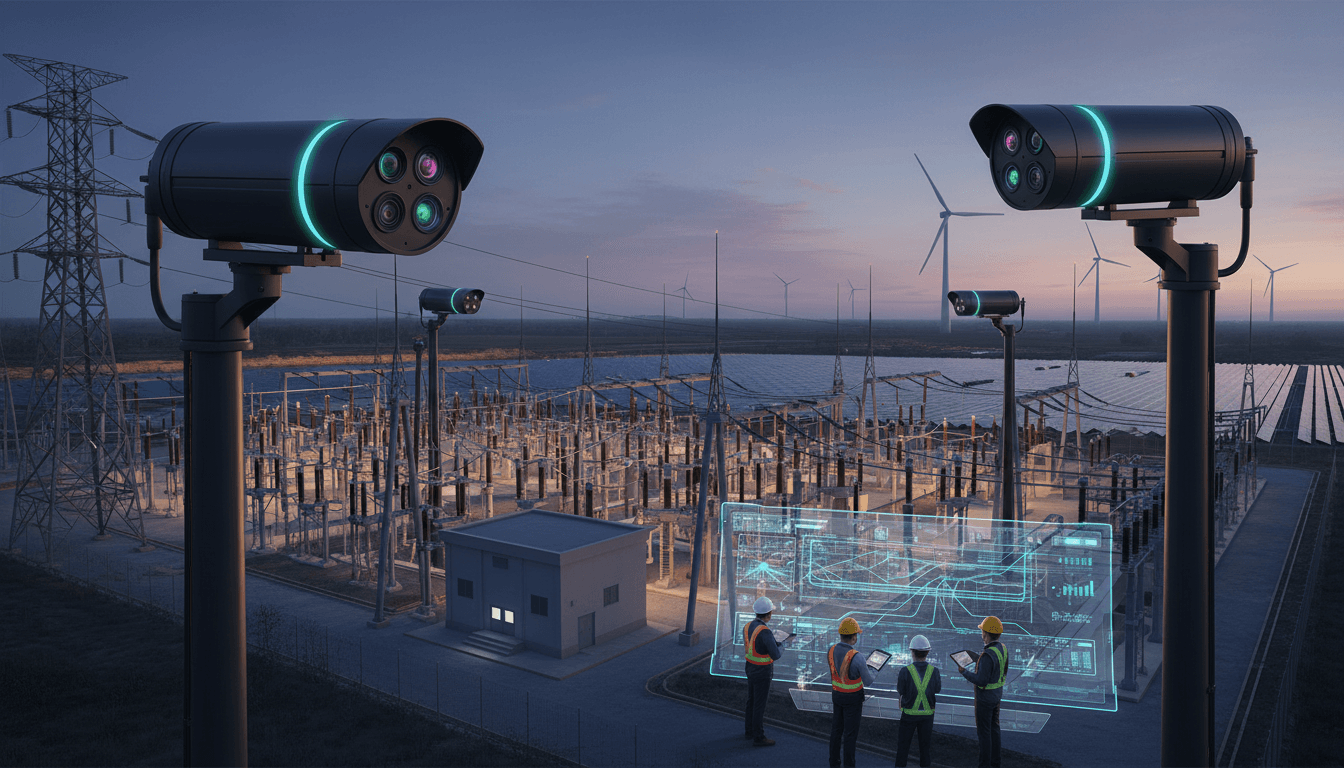
Technology Partners
Deploy AI algorithms that analyze data from security cameras in real-time. This enables proactive threat detection and response, significantly improving the security posture of energy assets and minimizing operational disruptions.
Industry Standards
Provide comprehensive training for security personnel on AI-driven protocols and technologies. This empowers staff to effectively utilize AI tools, ensuring robust surveillance and rapid response to incidents in the energy sector.
Internal R&D
Set up continuous monitoring systems that leverage AI insights for real-time analytics. This proactive measure enhances situational awareness and supports quick decision-making in addressing potential threats to infrastructure.
Cloud Platform
Conduct periodic evaluations of AI-driven security strategies to assess effectiveness and adapt to emerging threats. This ensures sustained resilience of energy operations and maximizes the benefits of AI technologies in security.
Industry Reports
Best Practices for Automotive Manufacturers
Implement Real-time Analytics Systems
- Impact : Enhances threat detection speed and accuracy
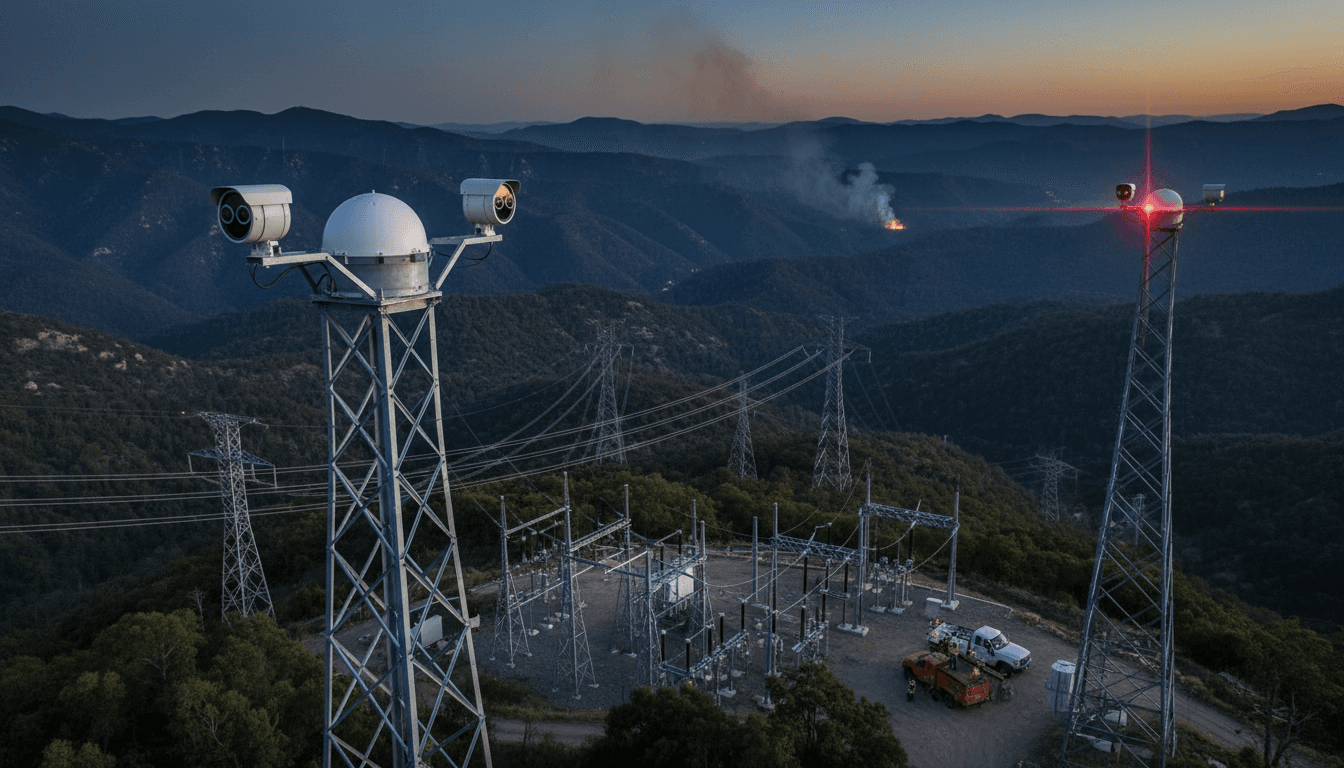
Example : Example: A utility company uses AI cameras to monitor grid infrastructure. When a potential breach is detected, alerts are generated in real time, allowing security teams to respond within minutes, minimizing any potential damage. - Impact : Improves incident response times significantly
Example : Example: An energy provider employs AI analytics to predict and identify incidents at substations. As a result, the average response time decreases from hours to under 30 minutes, significantly enhancing operational reliability. - Impact : Reduces operational downtime during threats
Example : Example: AI-driven analytics in a power plant provide immediate alerts for unusual activities around critical assets, allowing teams to proactively address issues before they escalate into serious security breaches. - Impact : Provides actionable insights for future prevention
Example : Example: A utility company analyzes past incidents with AI, leading to the development of a refined security protocol that reduces the likelihood of future threats by over 20%.
- Impact : High costs associated with system upgrades
Example : Example: A large energy firm invests heavily in upgrading AI camera systems but faces budget overruns that delay deployment, impacting their overall security strategy and leaving vulnerabilities exposed. - Impact : Potential for false positives in alerts
Example : Example: During initial testing, AI cameras falsely flag routine patrols as security threats, causing unnecessary alarms and wasted resources, leading to frustration among security personnel. - Impact : Dependence on skilled personnel for operations
Example : Example: The energy sector struggles to find skilled professionals to operate and maintain AI systems, risking prolonged downtimes and potential security gaps due to lack of expertise. - Impact : Integration issues with legacy systems
Example : Example: An energy company attempts to integrate AI cameras with outdated surveillance systems, resulting in compatibility issues that hamper data flow and effectiveness, delaying security enhancements.
Utilize Predictive Maintenance
- Impact : Minimizes unexpected equipment failures
Example : Example: A utility provider implements predictive maintenance for AI grid cameras . By analyzing historical failure data, they reduce unexpected downtime by 30%, ensuring consistent surveillance of critical infrastructure. - Impact : Extends lifespan of security assets
Example : Example: An energy company extends the lifespan of its AI cameras by 25% through predictive maintenance, resulting in lower replacement costs and uninterrupted monitoring of grid integrity. - Impact : Reduces maintenance costs significantly
Example : Example: By predicting potential failures in security systems, a utility reduces maintenance costs by 15% annually, allowing reinvestment into other critical security measures and technology upgrades. - Impact : Improves overall system reliability
Example : Example: Predictive analytics allows a power company to plan maintenance schedules effectively, leading to improved reliability of security systems and overall infrastructure resilience.
- Impact : Reliance on accurate data for predictions
Example : Example: A power utility finds that inaccurate historical data leads to flawed predictions, resulting in unexpected camera failures and security gaps, highlighting the need for data quality assurance. - Impact : Initial learning curve for AI systems
Example : Example: Employees at a utility company experience a steep learning curve when adopting a new AI predictive maintenance system, temporarily slowing operations and frustrating staff until proficiency is achieved. - Impact : Challenges in data integration and analysis
Example : Example: Integrating diverse data sources for predictive analysis proves challenging for a utility provider, delaying the benefits of AI and leaving them vulnerable to security breaches during the transition. - Impact : Potential for increased operational complexity
Example : Example: As a utility implements an advanced AI maintenance system, the increased complexity leads to operational confusion, necessitating additional training and support to maintain effective security operations.
Enhance Data Security Measures
- Impact : Protects sensitive surveillance data effectively
Example : Example: An energy firm implements advanced encryption for footage captured by AI cameras, ensuring that sensitive data remains protected from potential cyber-attacks, thereby enhancing overall security. - Impact : Ensures compliance with regulations
Example : Example: By adhering to strict compliance regulations for data security, a utility company avoids hefty fines and builds credibility with stakeholders, improving public trust in their operations. - Impact : Reduces risk of cyber threats
Example : Example: Regular audits of data security protocols in an energy company reveal vulnerabilities, leading to improved measures that decrease the risk of cyber threats by 40%. - Impact : Builds customer trust and confidence
Example : Example: A utility provider’s commitment to robust data security attracts new customers, as stakeholders feel assured their sensitive information is safe from breaches and misuse.
- Impact : Increased complexity in data management
Example : Example: A utility provider faces challenges managing the complexity of multiple security measures, leading to inefficiencies and potential oversights in data management, putting surveillance data at risk. - Impact : Potential compliance costs for regulations
Example : Example: Compliance with new regulations requires significant investment in data security infrastructure, straining the budget of a mid-sized utility firm and delaying other important projects. - Impact : Risk of data breaches and leaks
Example : Example: A power company experiences a data breach due to inadequate security measures, resulting in a loss of sensitive footage and a damaged reputation that takes years to rebuild. - Impact : Higher operational costs for security measures
Example : Example: The costs associated with implementing advanced data security protocols for AI cameras exceed initial projections, affecting the overall budget and diverting funds from other security initiatives.
Conduct Regular Training Programs
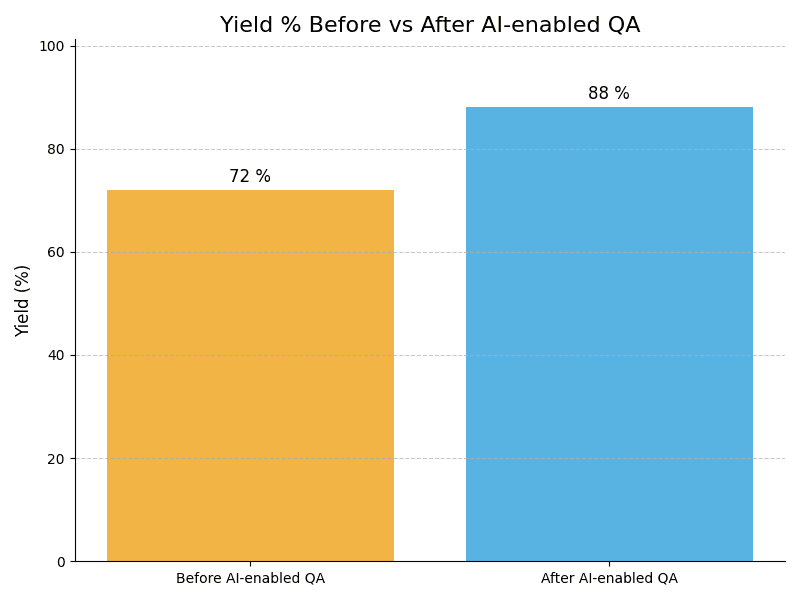
- Impact : Improves workforce competence with technology
Example : Example: A utility provider conducts regular training sessions on AI camera operations, resulting in a 50% decrease in human error incidents, improving overall surveillance effectiveness and response times. - Impact : Enhances team response to incidents
Example : Example: Following comprehensive training, a power plant team responds to an incident 40% faster, showcasing the direct impact of training on operational readiness and safety protocols. - Impact : Reduces human error in operations
Example : Example: Regular training on AI systems leads to a marked increase in employee confidence, resulting in fewer mistakes and a more proactive approach to security surveillance in the energy sector. - Impact : Encourages a culture of security awareness
Example : Example: By fostering a culture of security awareness through ongoing training, an energy company sees a significant decline in security breaches, creating a safer working environment for all personnel.
- Impact : Resource-intensive training efforts required
Example : Example: A utility company invests heavily in training programs, but the ongoing costs strain their budget, leading to cutbacks in other critical areas of security management. - Impact : Potential resistance from staff to change
Example : Example: Employees resist new training methods for AI systems, causing delays in the adoption of effective security practices and leading to frustration among management and staff alike. - Impact : Ongoing training needs can strain budgets
Example : Example: A mid-sized energy firm neglects to update training materials, resulting in staff using outdated knowledge that jeopardizes security protocols and diminishes the effectiveness of AI surveillance systems. - Impact : Risk of outdated knowledge without updates
Example : Example: Insufficient resources for training lead to a temporary decline in operational efficiency, as employees struggle to adapt to new AI technologies without adequate support and guidance.
Integrate Cross-Departmental Collaboration
- Impact : Fosters innovation through diverse perspectives
Example : Example: An energy provider creates cross-departmental teams to address security challenges, leading to innovative solutions that reduce vulnerability by 30%, demonstrating the power of collaborative efforts in security. - Impact : Improves incident reporting and response
Example : Example: By improving communication between IT and security departments, a utility company significantly enhances incident response times, reducing the average resolution time by 25%. - Impact : Enhances resource allocation for security
Example : Example: A power utility optimizes resource allocation by integrating insights from various departments, ensuring that security measures are not only effective but also cost-efficient, enhancing overall operational performance. - Impact : Strengthens overall security strategy
Example : Example: A collaborative approach to security strategy development at a utility firm strengthens their defenses against potential threats, leading to comprehensive protection across all operational areas.
- Impact : Challenges in aligning departmental goals
Example : Example: A utility struggles to align the goals of security and IT departments, leading to fragmented efforts in addressing vulnerabilities, ultimately resulting in security gaps and increased risks. - Impact : Increased complexity in communication channels
Example : Example: Cross-departmental communication at an energy firm becomes cumbersome, causing delays in incident reporting and response efforts, which ultimately undermines the effectiveness of security protocols. - Impact : Potential for conflict among teams
Example : Example: Clashes between departments over resources result in inefficiencies, as critical security projects are delayed due to unresolved conflicts, jeopardizing overall operational safety. - Impact : Resource allocation may become inefficient
Example : Example: A poorly managed resource allocation strategy leads to some departments receiving excess funding while others lack necessary support, resulting in imbalanced security measures across the organization.
Leverage Cloud-based Solutions
- Impact : Facilitates remote monitoring of assets
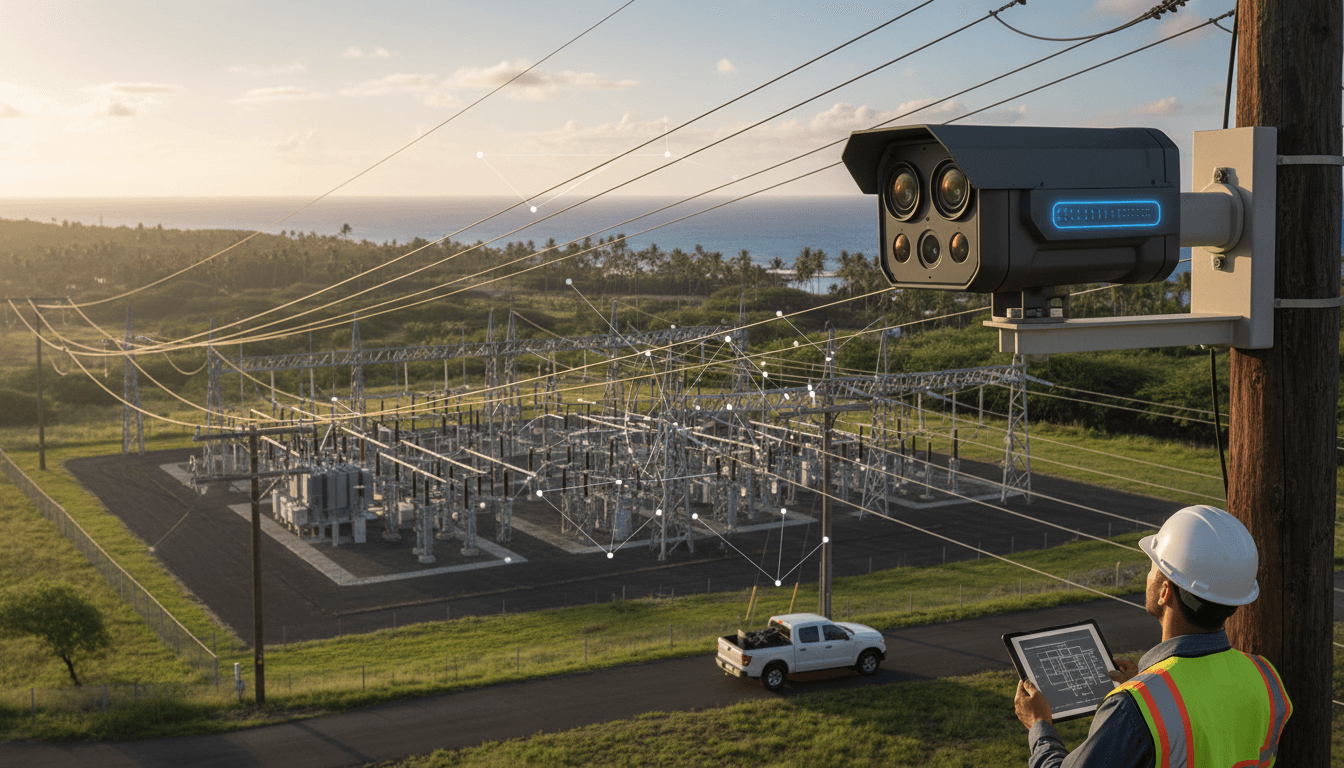
Example : Example: A utility company leverages cloud-based solutions to monitor grid security remotely, allowing real-time insights that enhance response capabilities and reduce the need for on-site personnel. - Impact : Enhances data storage capabilities
Example : Example: By utilizing cloud storage for surveillance footage, an energy provider significantly increases its data retention capabilities without the need for expensive on-premises infrastructure, saving costs. - Impact : Improves scalability of security systems
Example : Example: A power company scales its AI security solutions more effectively through cloud solutions, enabling quick adjustments to security measures without significant logistical challenges or delays. - Impact : Reduces costs related to infrastructure
Example : Example: Transitioning to cloud-based security systems allows a utility to cut infrastructure costs by 20%, freeing up funds for other critical security initiatives and improvements.
- Impact : Dependence on internet connectivity
Example : Example: A utility provider faces challenges during a storm when internet connectivity is lost, leaving AI cameras unable to transmit data, which compromises security monitoring in critical areas. - Impact : Potential data sovereignty issues
Example : Example: An energy company grapples with data sovereignty issues when storing sensitive surveillance data in the cloud, raising concerns about compliance with international regulations and laws. - Impact : Cybersecurity risks with cloud systems
Example : Example: A cyberattack on a cloud service provider exposes vulnerabilities in an energy firm's security system, prompting urgent reevaluation of their cloud strategy and resulting in costly downtime. - Impact : Ongoing costs for cloud services
Example : Example: The ongoing costs for cloud services strain a utility's budget, leading to tough decisions about resource allocation and potentially affecting other critical security measures.
We're partnering with Qualcomm to implement their AI technology in drones and sensors for grid inspection, which will make our processes much more efficient and enhance security monitoring.
– Scott Monteith, Representative from Avalon Advanced MaterialsCompliance Case Studies
_case_study.png&w=3840&q=75)
Embrace the future of energy security. Leverage AI Grid Security Cameras to enhance safety, efficiency, and reliability. Don’t let your operations fall behind—act today!
Take Test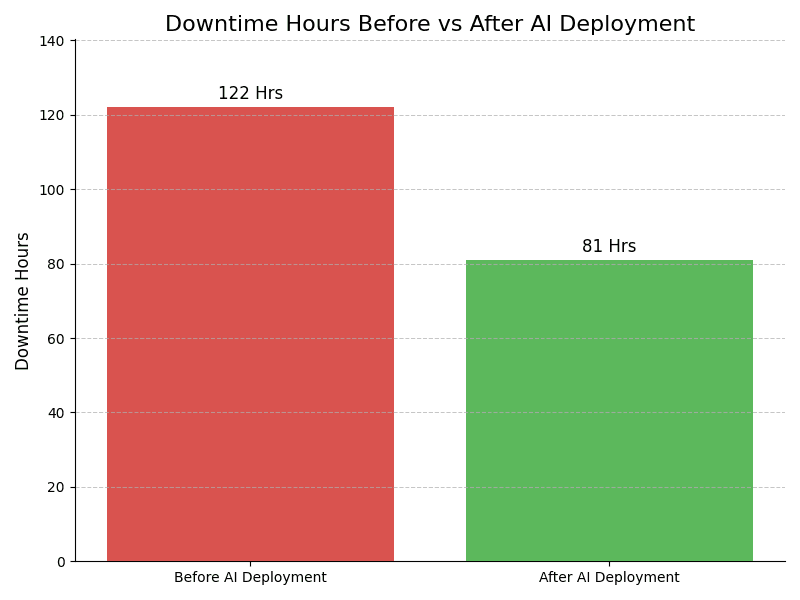
Leadership Challenges & Opportunities
Data Privacy Concerns
Utilize AI Grid Security Cameras with advanced encryption and data masking features to protect sensitive information. Implement strict access controls and regular audits to ensure compliance with data privacy regulations. This approach mitigates risks while enhancing surveillance capabilities across Energy and Utilities operations.
Infrastructure Vulnerability
Integrate AI Grid Security Cameras with real-time threat detection algorithms to identify potential vulnerabilities in Energy and Utilities infrastructure. Employ predictive analytics to preemptively address weaknesses and reinforce security measures, ensuring a more resilient operational environment for critical assets.
Change Management Resistance
Facilitate the adoption of AI Grid Security Cameras by promoting a culture of innovation within the organization. Conduct workshops and training sessions to demonstrate the technology's benefits, foster stakeholder engagement, and address resistance, ensuring a smoother transition and increased buy-in from employees.
Skill Shortages in AI
Address skill shortages by partnering with educational institutions to create training programs focused on AI Grid Security Cameras technology. Implement mentorship initiatives and internal certification to build a skilled workforce, ensuring that the organization is equipped to effectively utilize advanced surveillance solutions.
Assess how well your AI initiatives align with your business goals
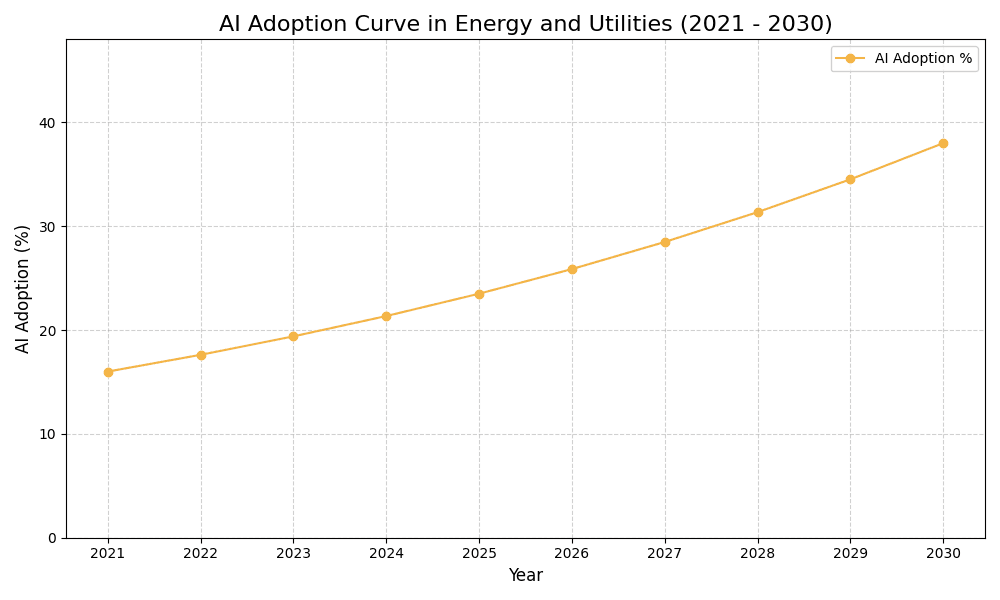
AI Adoption Graph
AI Use Case vs ROI Timeline
| AI Use Case | Description | Typical ROI Timeline | Expected ROI Impact |
|---|---|---|---|
| Real-time Threat Detection | AI-powered cameras analyze video feeds to identify suspicious activities instantly. For example, an AI camera detects unauthorized access to a substation, triggering alerts to security personnel for immediate action. | 6-12 months | High |
| Predictive Maintenance Alerts | AI analyzes footage to spot maintenance issues before they escalate. For example, it identifies wear and tear on equipment visible in video, allowing preemptive repairs and minimizing downtime. | 12-18 months | Medium-High |
| Automated Incident Reporting | AI systems automatically document security incidents by analyzing camera feeds. For example, when an incident occurs, the system generates a report with video evidence, streamlining the review process for security teams. | 6-12 months | Medium |
| Enhanced Perimeter Security | AI cameras use facial recognition to monitor restricted areas. For example, they can alert teams when unauthorized individuals are detected around critical infrastructure, improving response times. | 12-18 months | High |
Glossary
Work with Atomic Loops to architect your AI implementation roadmap — from PoC to enterprise scale.
Contact NowFrequently Asked Questions
- AI Grid Security Cameras enhance security through real-time video analytics and monitoring.
- They reduce response times to potential threats, improving overall operational safety.
- The technology helps in preventing infrastructure damage and operational disruptions.
- Organizations benefit from data-driven insights that inform strategic decision-making.
- This leads to improved risk management and compliance with regulatory standards.
- Begin by assessing your current security infrastructure and identifying gaps.
- Engage with technology partners to evaluate suitable AI solutions for your needs.
- Pilot projects can help demonstrate value before full-scale implementation.
- Allocate necessary resources, including budget and personnel, for the project.
- Training staff on AI technology will ensure smoother integration and operation.
- Organizations can track reductions in security incidents and response times.
- Improved monitoring capabilities lead to better resource allocation and efficiency.
- Success metrics may include enhanced compliance with industry standards and regulations.
- Customer satisfaction often increases due to enhanced service reliability and safety.
- Long-term, organizations may see reduced operational costs from better risk management.
- Common challenges include integration with legacy systems and data silos.
- Employee resistance to new technologies can hinder the implementation process.
- Regular training and change management strategies can mitigate these issues.
- Data privacy and compliance concerns may also pose significant challenges.
- Developing a clear strategy for risk management is crucial for overcoming obstacles.
- Investing in AI enhances security and operational efficiency across the grid.
- AI technology enables proactive threat detection, reducing potential damages.
- Companies gain competitive advantages through improved service delivery and safety.
- The investment can lead to long-term cost savings through optimized operations.
- Enhanced compliance with regulatory requirements helps mitigate legal risks.
- Organizations should consider implementation during scheduled upgrades or expansions.
- Assessing the current security landscape can identify urgent needs for improvement.
- Timely adoption can prevent potential security breaches or operational disruptions.
- Engagement with stakeholders can help align timing with business objectives.
- Regular reviews of security strategies ensure readiness for immediate implementation.